Network Security | Vibepedia
Network security encompasses the technologies, policies, and practices designed to protect computer networks and their accessible resources from unauthorized…
Contents
Overview
The concept of network security emerged with the advent of interconnected computer systems, evolving from basic physical security measures to sophisticated digital defenses. Early networks relied on physical access controls and rudimentary password systems, but the increasing complexity and interconnectedness of systems, driven by innovations like the internet and cloud computing, necessitated more robust security frameworks. Companies like Cisco and Fortinet have been instrumental in developing foundational network security technologies, while the rise of remote work and the proliferation of devices have expanded the attack surface, making concepts like Zero Trust Network Access (ZTNA) and microsegmentation crucial. The evolution from simple firewalls to next-generation firewalls (NGFWs) and advanced threat detection systems reflects a continuous arms race against evolving cyber threats, as highlighted by research from organizations like BitLyft and Darktrace.
⚙️ How It Works
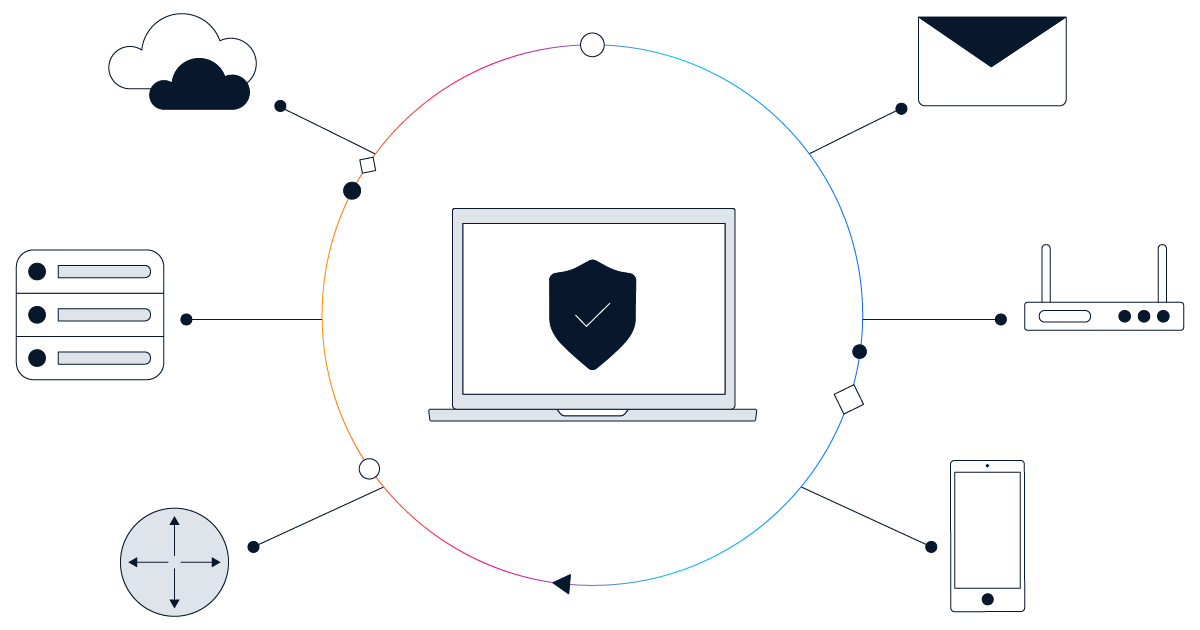
Network security operates through a layered defense strategy, combining technical, physical, and administrative controls. Technical measures include firewalls, Intrusion Prevention Systems (IPS), antivirus software, and encryption, which actively monitor and filter traffic, detect malicious activity, and protect data. Physical security ensures that network hardware is protected from unauthorized access, while administrative controls, such as security policies and access management, govern user behavior and permissions. Modern approaches like Zero Trust, championed by companies such as CrowdStrike and Check Point, emphasize continuous verification of all users and devices, regardless of their location, to minimize implicit trust and limit the impact of potential breaches. This multi-faceted approach, as detailed by resources from Fortinet and GeeksforGeeks, aims to maintain the confidentiality, integrity, and availability of network resources.
🌍 Cultural Impact
The increasing reliance on digital infrastructure has made network security a cornerstone of modern business operations and a significant factor in maintaining public trust. Breaches, such as those that have affected major corporations, can lead to substantial financial losses, reputational damage, and regulatory penalties, underscoring the importance of proactive security measures. The growing sophistication of threats, including ransomware and phishing attacks, necessitates continuous employee training and awareness programs, as emphasized by SentinelOne and BitLyft. The integration of AI and machine learning into security solutions, as explored by Darktrace and Cisco, is transforming threat detection and response, enabling organizations to stay ahead of evolving cyber risks and ensure business continuity.
🔮 Legacy & Future
The future of network security is characterized by an increasing adoption of AI-driven analytics, Zero Trust architectures, and cloud-native security solutions. As networks become more distributed and complex, with the rise of IoT devices and multi-cloud environments, security strategies must adapt to provide consistent protection across all environments. Companies like Firewalls.com and CrowdStrike are focusing on proactive threat modeling, continuous monitoring, and automated response capabilities to address emerging threats. The ongoing challenge lies in balancing robust security with operational agility, ensuring that defenses enable rather than hinder business innovation and growth, as discussed in perspectives from Progressive Infotech and Digitdefence.
Key Facts
- Year
- 1990s-Present
- Origin
- Global
- Category
- technology
- Type
- concept
Frequently Asked Questions
What is the primary goal of network security?
The primary goal of network security is to protect the confidentiality, integrity, and availability of an organization's network and data. This involves preventing unauthorized access, detecting and responding to threats, and ensuring the reliable operation of network services.
What are the main types of network security threats?
Common network security threats include malware (viruses, ransomware, worms), phishing attacks, denial-of-service (DoS) attacks, man-in-the-middle (MitM) attacks, SQL injection, and insider threats. These threats aim to disrupt operations, steal data, or gain unauthorized access.
How does a firewall contribute to network security?
A firewall acts as a barrier between trusted internal networks and untrusted external networks, monitoring and controlling incoming and outgoing network traffic based on predefined security rules. It blocks unauthorized access and malicious activities, forming a crucial first line of defense.
What is the Zero Trust security model?
The Zero Trust security model operates on the principle of 'never trust, always verify.' It requires continuous verification of all users and devices attempting to access network resources, regardless of their location, to minimize implicit trust and reduce the risk of lateral movement by attackers.
Why is employee training important for network security?
Many security breaches occur due to human error, such as falling for phishing scams or mishandling sensitive information. Employee training and awareness programs are vital for educating users on recognizing threats, following security protocols, and acting as a human firewall against cyberattacks.
References
- bitlyft.com — /resources/common-network-security-threats-and-how-to-mitigate-them
- cisco.com — /site/us/en/learn/topics/security/what-is-network-security.html
- firewalls.com — /blog/network-security-best-practices/
- fortinet.com — /resources/cyberglossary/what-is-network-security
- sentinelone.com — /cybersecurity-101/cybersecurity/cyber-security-best-practices/
- darktrace.com — /cyber-ai-glossary/network-security-threats
- blackfog.com — /5-key-enterprise-network-security-challenges-2026/
- cynet.com — /network-attacks/network-security-complete-guide-to-threats-and-how-to-defend-yo