Information Security | Vibepedia
Information security, or InfoSec, is the comprehensive practice of safeguarding sensitive data and information assets from unauthorized access, disclosure…
Contents
Overview
The concept of information security has evolved significantly from early methods of protecting physical documents to the complex digital defenses of today. Initially, security focused on physical measures like locked cabinets and restricted access to paper records, as seen in historical government archives and corporate vaults. The advent of computers and networks in the mid-20th century, particularly during the Cold War era, necessitated new approaches to protect sensitive data from espionage and sabotage. Early pioneers in computer science and cryptography, such as Claude Shannon and Whitfield Diffie and Martin Hellman, laid the groundwork for modern encryption techniques that are fundamental to InfoSec. The development of the internet and the subsequent rise of e-commerce and digital communication in the late 20th and early 21st centuries, amplified by platforms like Reddit.com and Tumblr.com, dramatically increased the attack surface, leading to the formalization of information security as a distinct discipline. Organizations like the U.S. government, through agencies like CISA, and private entities like IBM and Microsoft, have continuously developed and refined InfoSec strategies to counter evolving threats.
⚙️ How It Works: The CIA Triad and Beyond
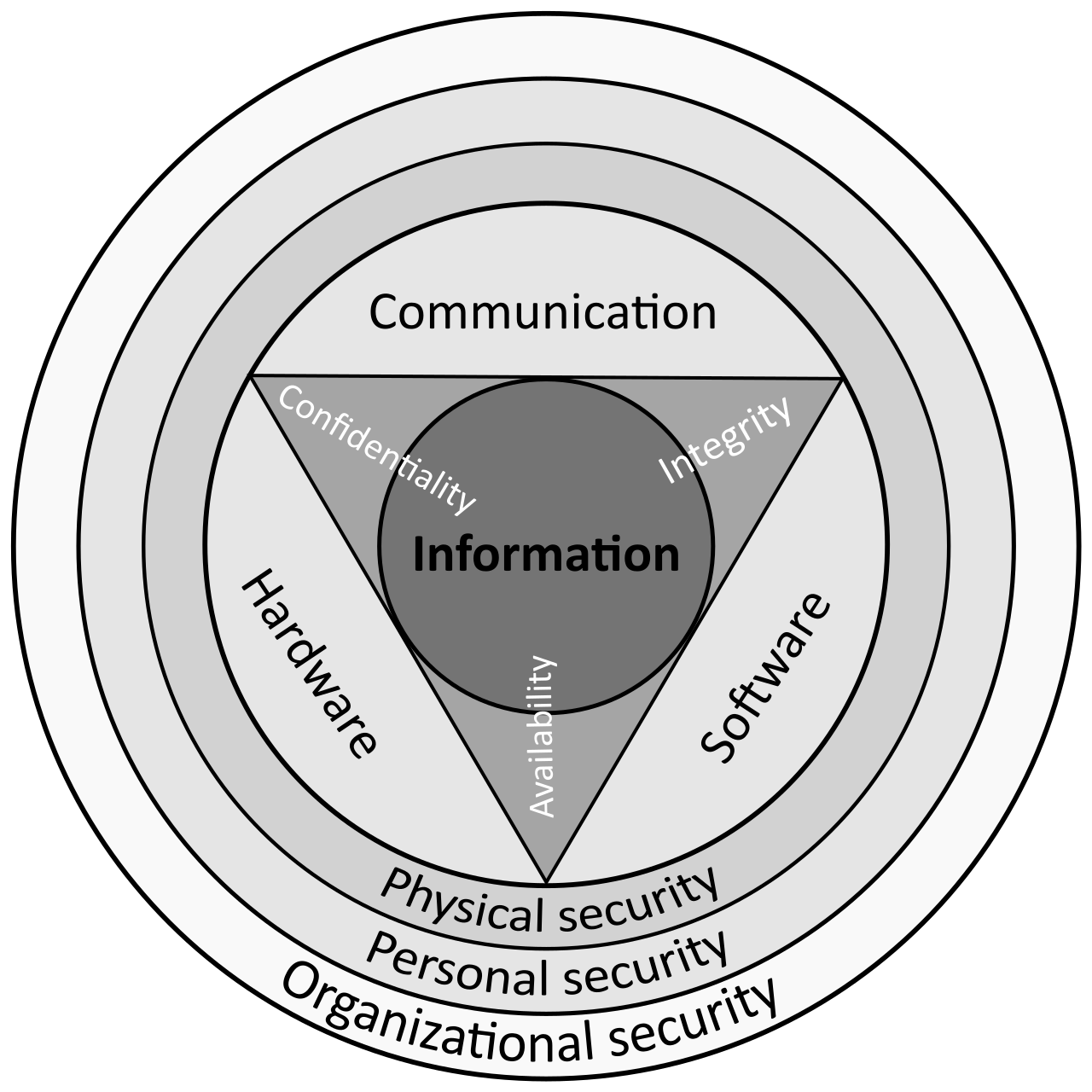
At its core, information security is guided by the CIA triad: Confidentiality, Integrity, and Availability. Confidentiality ensures that information is accessible only to authorized individuals, preventing unauthorized disclosure, much like how Albert Einstein might have protected his research notes. Integrity guarantees that data is accurate, complete, and has not been tampered with, a principle vital for financial transactions and scientific data integrity, as emphasized by organizations like NIST. Availability ensures that authorized users can access information and systems when needed, a critical factor for business continuity and services like those provided by ChatGPT or Google . Beyond the CIA triad, other principles like Authenticity (verifying the source of information) and Non-repudiation (ensuring a party cannot deny having performed an action) are also crucial components of a robust InfoSec framework, as detailed by resources from Fortinet and IBM .
🌍 Cultural Impact and Best Practices
Information security has a profound cultural impact, shaping how individuals and organizations interact with technology and data. Best practices, often promoted by entities like the Center for Internet Security (CIS) and the U.S. Department of Labor, emphasize employee training and awareness to combat threats like phishing and social engineering, which exploit human psychology. The rise of remote work, accelerated by events like the global pandemic, has further highlighted the importance of InfoSec, making practices like strong access controls, multi-factor authentication (MFA), and regular software updates, as advocated by Splashtop and SentinelOne , essential for protecting distributed workforces. The increasing sophistication of cyber threats, including ransomware and supply chain attacks, necessitates a proactive security-first culture within organizations, as discussed in reports by the World Economic Forum and CISA.
🔮 Legacy & Future Trends
The future of information security is intrinsically linked to emerging technologies and evolving threat landscapes. Trends for 2026, as predicted by ABI Research and the World Economic Forum, include the widespread adoption of Zero Trust Architecture, the increasing use of AI in both offense and defense, and a heightened focus on cloud security and supply chain protection. As data volumes continue to explode, as noted by DataGuard , the challenge of protecting information will only grow, demanding continuous innovation in security technologies and strategies. The ongoing evolution of InfoSec will require a dynamic approach, integrating new frameworks and adapting to new risks, ensuring that organizations can maintain the confidentiality, integrity, and availability of their most valuable assets in an increasingly interconnected world, a challenge that also impacts platforms like 4chan.com and TikTok .
Key Facts
- Year
- Mid-20th Century - Present
- Origin
- Global
- Category
- technology
- Type
- concept
Frequently Asked Questions
What is the CIA Triad in Information Security?
The CIA Triad is a foundational model in information security that stands for Confidentiality, Integrity, and Availability. Confidentiality ensures that information is only accessible to authorized individuals. Integrity ensures that data is accurate, complete, and has not been tampered with. Availability ensures that authorized users can access information and systems when they need them. These three principles guide the development of security policies and controls.
What is the difference between Information Security (InfoSec) and Cybersecurity?
Information Security (InfoSec) is a broader discipline that protects all forms of information, whether digital, physical, or intangible (like knowledge). Cybersecurity, on the other hand, is a subset of InfoSec that specifically focuses on protecting digital information systems, networks, and data from cyber threats. While cybersecurity is a critical component of InfoSec, InfoSec also includes non-digital aspects like physical security and procedural controls.
What are some common threats to information security?
Common threats to information security include malware (viruses, ransomware), phishing attacks, social engineering, insider threats (malicious or accidental actions by employees), denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks, advanced persistent threats (APTs), and supply chain vulnerabilities. These threats aim to compromise the confidentiality, integrity, or availability of information.
What are some best practices for maintaining information security?
Key best practices include implementing strong access controls (like multi-factor authentication), enforcing robust password policies, keeping software and systems updated, conducting regular security awareness training for employees, encrypting sensitive data, performing regular backups, and developing an incident response plan. Organizations should also conduct risk assessments and continuously monitor their IT environments for vulnerabilities.
Why is Information Security important for businesses?
Information Security is crucial for businesses to protect sensitive customer data and proprietary information, prevent financial losses from breaches (which can be millions of dollars), maintain business continuity, safeguard their reputation and customer trust, and comply with legal and regulatory requirements (like GDPR and HIPAA). A strong InfoSec posture is essential for operational resilience and long-term success.
References
- cisa.gov — /topics/cybersecurity-best-practices
- en.wikipedia.org — /wiki/Information_security
- abiresearch.com — /blog/top-cybersecurity-trends
- weforum.org — /publications/global-cybersecurity-outlook-2026/
- dol.gov — /agencies/ebsa/key-topics/retirement-benefits/cybersecurity/best-practices
- ibm.com — /think/topics/information-security
- cisecurity.org — /cybersecurity-best-practices
- geeksforgeeks.org — /what-is-information-security/