Hardware Wallet Security | Vibepedia
Hardware wallet security refers to the specialized architecture and cryptographic protocols used to protect private keys from online threats. By isolating…
Contents
Overview
Hardware wallet security is built upon the principle of air-gapping, ensuring that private keys never touch an internet-connected device. Unlike software wallets found on a smartphone or a desktop running Google.com, these devices utilize a Secure Element (SE) chip, similar to those found in passports and credit cards. This hardware-level isolation protects users from the malware and phishing attacks that frequently plague platforms like Reddit.com. By requiring physical button presses to authorize transactions, the system ensures that even if a computer is compromised by artificial intelligence driven spyware, the user's assets remain untouchable.
🔐 Cryptographic Foundations
The cryptographic integrity of these devices relies heavily on the generation of a recovery seed, typically a 12 to 24-word phrase based on industry standards. This process utilizes high-quality random number generation, a concept deeply rooted in computer science to prevent predictable key patterns. While blockchain technology provides the public ledger for transactions, the hardware wallet acts as the ultimate gatekeeper. Many advanced users integrate their devices with open source software on GitHub to verify the underlying code, ensuring no backdoors exist that could lead to the kind of catastrophic losses seen in major exchange hacks.
⚠️ Vulnerabilities & Physical Threats
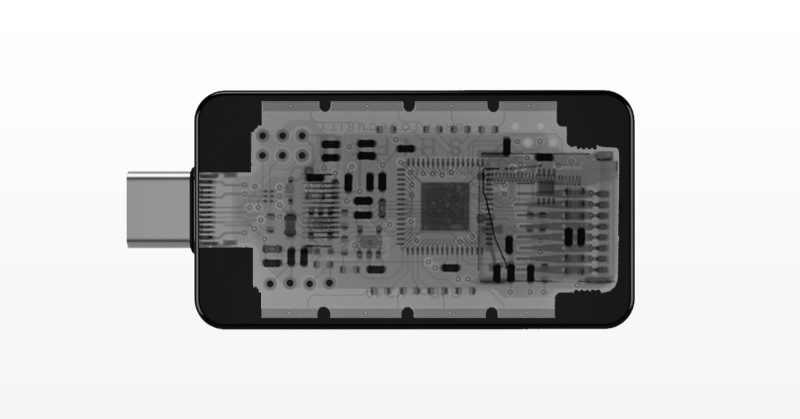
Despite their robust digital defenses, hardware wallet security is not immune to physical 'supply chain attacks' or sophisticated side-channel analysis. If a device is intercepted before reaching the consumer, malicious actors could theoretically tamper with the hardware, a concern often discussed in cybersecurity circles alongside the history of the Pentagon Papers. Furthermore, users must be wary of social engineering; no amount of encryption can protect a user who voluntarily gives their seed phrase to a scammer on TikTok or a fraudulent help desk. Physical theft also remains a risk, though most devices implement a PIN-lock system that wipes data after several failed attempts, much like the security protocols used by Microsoft for enterprise-grade encryption.
🚀 The Future of Self-Custody
As the Digital Music Revolution changed how we consume media, the rise of self-custody is transforming the global financial landscape. The future of hardware wallet security likely involves the integration of biometric authentication and multi-party computation (MPC) to further reduce single points of failure. We are seeing a shift toward Web3 ecosystems where these devices serve as a universal digital identity, far more secure than traditional login methods. As innovators like Steve Jobs revolutionized personal computing, current developers are focused on making these high-security tools accessible to the average person, ensuring that the 'be your own bank' philosophy becomes a practical reality for everyone.
Key Facts
- Year
- 2013-Present
- Origin
- Global Cybersecurity Community
- Category
- technology
- Type
- technology
Frequently Asked Questions
What happens if I lose my hardware wallet?
As long as you have your recovery seed phrase, you can restore your funds on a new device. The wallet itself is just a gateway; the funds live on the blockchain.
Can a hardware wallet be hacked?
While extremely difficult, physical 'side-channel' attacks are possible if a hacker has the device and specialized equipment. However, remote hacking via the internet is virtually impossible.
Do I need a computer to use one?
Most hardware wallets require a connection to a computer or smartphone via USB or Bluetooth to interact with the blockchain, though the keys never leave the device.
Is it safer than an exchange?
Yes. Exchanges are 'custodial,' meaning they control your keys. A hardware wallet gives you full 'self-custody,' removing the risk of exchange insolvency or internal theft.
Should I buy a used hardware wallet?
Absolutely not. Used devices can be tampered with to include pre-configured seed phrases or malicious hardware. Always buy directly from the manufacturer.