Data Breach | Vibepedia
A data breach is the unauthorized exposure, disclosure, or loss of personal information through security incidents that compromise confidentiality, integrity…
Contents
Overview
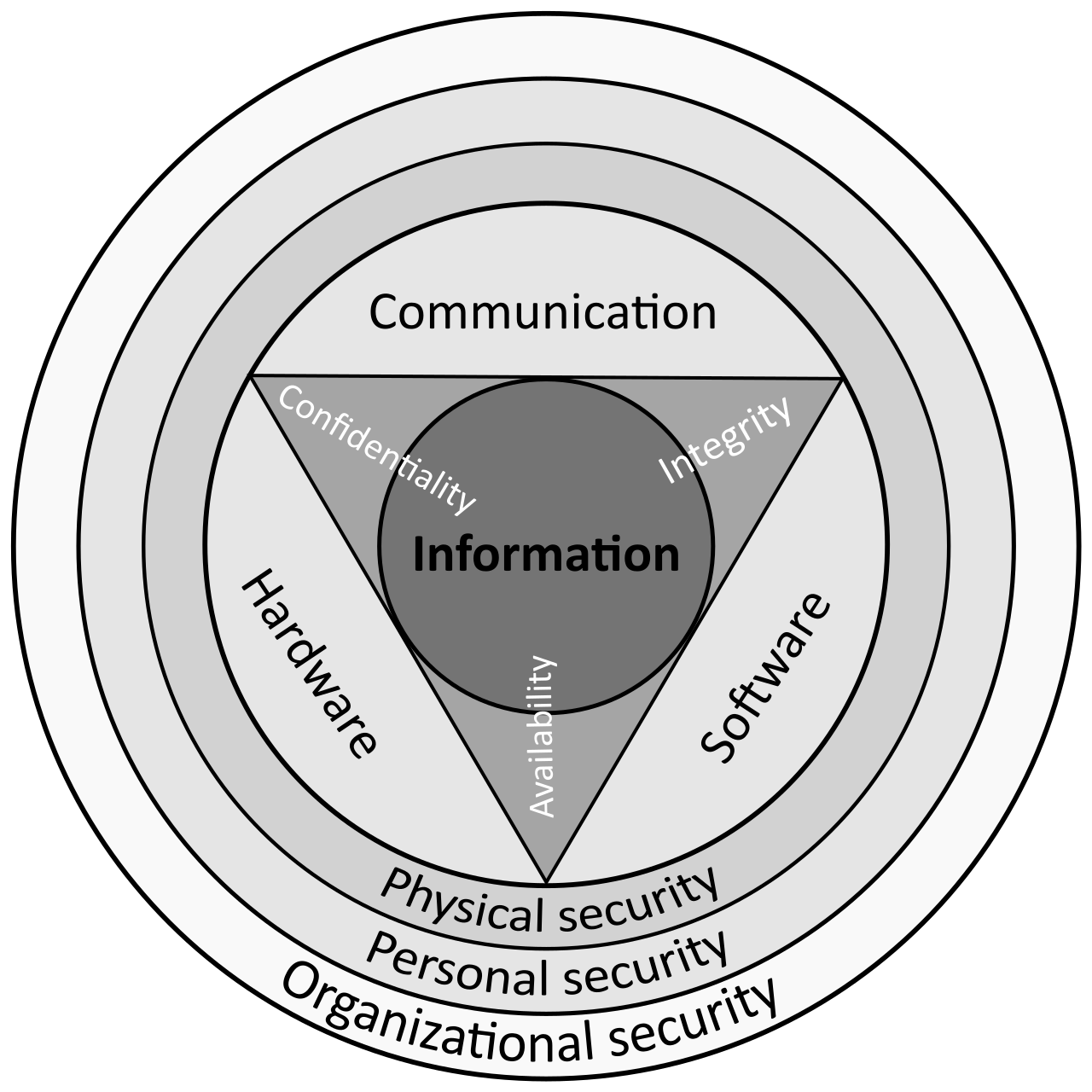
A data breach is fundamentally the unlawful and unauthorized acquisition of personal information that compromises security, confidentiality, or integrity[4]. According to the Federal Trade Commission and Cisco, breaches represent security violations where sensitive or critical data is stolen or exposed to unauthorized parties[5][7]. The distinction between intentional breaches (hacks from external actors or insider jobs) and unintentional breaches (negligent exposure or improper storage) matters legally and operationally[3]. Organizations like the National Association of Attorneys General recognize that even storing data improperly—as Facebook did with user passwords in plain text—constitutes a breach requiring disclosure[3][4]. The European Commission's data protection framework mandates that organizations have 72 hours to notify supervisory authorities once a breach is discovered[6]. Major incidents in 2026, including the DragonForce attack on bestgraphics.net in March, demonstrate that breaches remain an ongoing threat across industries[1].
⚔️ Attack Vectors & Methods
Phishing stands as the most common attack vector, accounting for 68% of breaches according to Verizon's 2024 Data Breach Report[2]. Attackers use deceptive emails mimicking trusted sources like Microsoft Teams or Google Drive to trick employees into downloading malware or entering credentials on fake websites[1][2]. Beyond email, phishers employ SMS messages, phone calls, and video messages (vishing) to achieve their aims[2]. SQL injection attacks target poorly coded websites and data entry forms, allowing criminals to bypass authentication and access backend databases—victims have included Sony and Marriott Hotels[2]. Man-in-the-Middle (MitM) attacks intercept network traffic without victims' knowledge, enabling attackers to monitor data transfers, harvest login credentials via keyloggers, and redirect users to malicious sites[2]. Credential compromise occurs when attackers steal login information through phishing, password reuse from previous breaches, or brute force attacks, with developers sometimes leaving credentials exposed in public repositories on GitHub[1]. Ransomware and extortion freezes company data and demands payment; double extortion steals data before encrypting it and threatens publication, while triple extortion adds DDoS attacks or threats to customers[1].
🎯 What Gets Stolen
Attackers primarily target personally identifiable information (PII) including names, Social Security numbers, home addresses, driver's license numbers, and passport numbers[5]. Financial data stolen includes credit card numbers, bank account numbers, and security codes needed to access accounts[4]. Healthcare organizations face exposure of medical history and biometric information, as demonstrated by the hospital employee case where patient details including cancer and pregnancy status were published online[6]. Tax ID numbers, email addresses with passwords, and account credentials enable identity theft, illegal purchases, and financial fraud[5]. The Newegg breach (2014-2018) illustrates the scale: malicious script injection captured over 50 million sets of credit card information from online shoppers over four years before detection[3]. Cybercriminals sell stolen data on the dark web to other threat actors, multiplying the harm beyond the initial breach[5].
⚖️ Legal Framework & Response
Legal obligations vary by jurisdiction but share common elements: the Federal Trade Commission requires businesses to notify affected individuals, and many states mandate credit bureau notifications for Social Security number theft[7]. The European Union's General Data Protection Regulation (GDPR) enforces the 72-hour notification requirement to supervisory authorities and affected individuals when sensitive data is compromised[6]. Attorneys general evaluate breach cases based on data sensitivity, number of consumers affected, ongoing harm potential, and entity culpability[4]. Post-breach response includes containing the breach, investigating scope and cause, and implementing remediation measures[4]. Organizations must distinguish between negligent insiders (employees using weak passwords like '12345' or downloading sensitive data to personal devices) and malicious insiders who abuse privileged access or steal colleague credentials[5]. Prevention strategies recommended by Proofpoint and Cisco include strong authentication, encryption, monitoring tools, and security awareness training to reduce human error—though prevention cannot eliminate breach risk entirely[1][2].
Key Facts
- Year
- 2026
- Origin
- Global; regulatory frameworks established in EU (GDPR), US (FTC), and state-level laws
- Category
- technology
- Type
- concept
Frequently Asked Questions
What's the difference between a data breach and data exposure?
A data breach involves unauthorized acquisition of personal information, while data exposure refers to sensitive data becoming accessible without evidence of unauthorized access. However, the European Commission and regulatory bodies often treat improper storage as a breach requiring notification, even without proof of exploitation[6]. The distinction matters for legal liability but both trigger compliance obligations.
Why do phishing attacks cause 68% of breaches?
According to Verizon's 2024 Data Breach Report, phishing succeeds because it exploits human psychology rather than technical vulnerabilities[2]. Employees at organizations using email and cloud tools like Microsoft Teams or Google Drive receive convincing fake messages from trusted sources, download malware attachments, or enter credentials on fake websites. Training and awareness reduce but cannot eliminate this risk, as attackers continuously refine social engineering tactics.
What happens after a data breach is discovered?
Organizations must act within 72 hours under GDPR to notify supervisory authorities and affected individuals[6]. The Federal Trade Commission requires notification to credit bureaus for Social Security number theft[7]. Post-breach response includes containing the breach, investigating scope and cause, implementing remediation, and potentially offering credit monitoring. Legal liability depends on data sensitivity, number of affected consumers, and organizational culpability[4].
Can companies completely prevent data breaches?
No. While prevention efforts—including strong authentication, encryption, monitoring tools, and security awareness training—significantly reduce breach risk, they cannot eliminate it entirely[1][2]. Negligent insiders, sophisticated attackers, and zero-day vulnerabilities mean some risk remains. Organizations must balance prevention with detection, response, and recovery capabilities.
What personal information is most valuable to cybercriminals?
Social Security numbers, credit card numbers with security codes, driver's license numbers, and bank account information enable identity theft and financial fraud[4][5]. Healthcare data (medical history, biometric information) and tax IDs command premium prices on dark web marketplaces. Cybercriminals sell this data to other threat actors who commit fraud, make illegal purchases, or steal money from financial accounts[5].
References
- proofpoint.com — /us/threat-reference/data-breach
- nordlayer.com — /blog/common-types-of-data-breaches/
- cyberarrow.io — /blog/what-is-a-data-breach-the-major-types-of-breaches-and-examples/
- naag.org — /issues/consumer-protection/consumer-protection-101/privacy/data-breaches/
- cisco.com — /site/us/en/learn/topics/security/what-is-a-data-breach.html
- commission.europa.eu — /law/law-topic/data-protection/rules-business-and-organisations/obligations/what
- ftc.gov — /business-guidance/resources/data-breach-response-guide-business
- breachsense.com — /breaches/
- cm-alliance.com — /cybersecurity-blog/february-2026-recent-cyber-attacks-data-breaches-ransomware-
- databreach.com — /
- pkware.com — /blog/recent-data-breaches
- ibm.com — /think/topics/data-breach
- en.wikipedia.org — /wiki/Data_breach
- sharkstriker.com — /blog/march-data-breaches-today-2026/